(The Quantum Algorithms Institute is an IYQ sponsor.)
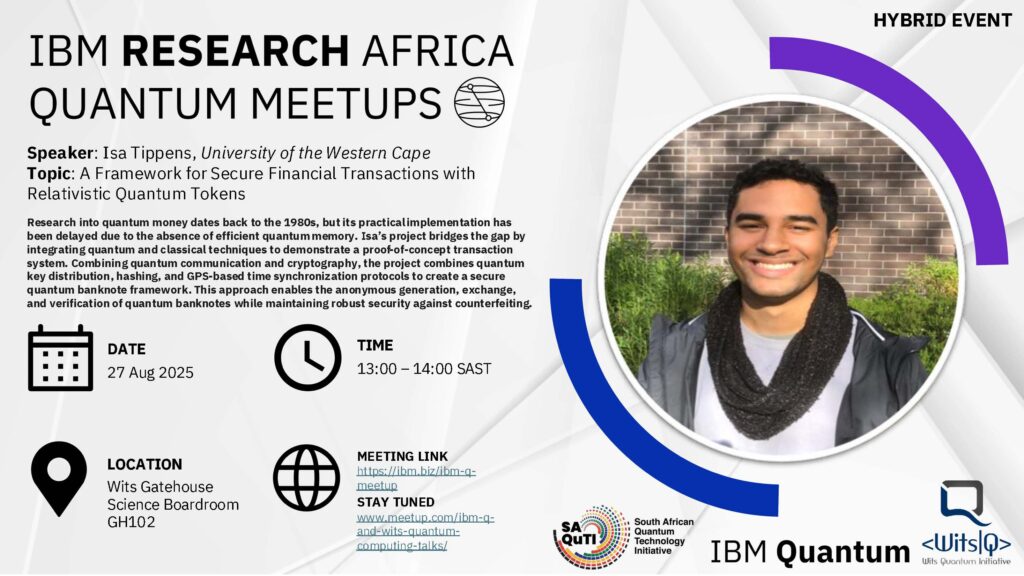
Quantum computers are a powerful emerging technology that could solve some of the world’s most complex problems. Unfortunately, one of those problems includes breaking our most widely used encryption algorithms, compromising massive amounts of data worldwide.
But in 2025, this should not be news. The quantum threat to cybersecurity has been a hot topic for years, with many organizations working to remediate it. Recently, the US National Institute of Standards and Technology (NIST) has released three standardized “quantum safe” encryption algorithms, marking a huge milestone in post-quantum cybersecurity development. So, with these new safe encryption mechanisms, isn’t this threat now neutralized? Unfortunately, not yet.
The emergence of new encryption standards and national migration guidelines is only the first step in the post-quantum security process; getting organizations to implement these new standards in time, before large-scale quantum computers emerge, is a far more daunting task.
Due to the unpredictable nature of quantum computing progress, skepticism about the validity of the quantum threat, and, most importantly, the lack of a distinct Q-Day deadline, the atmosphere surrounding post-quantum cryptography migration shows a considerable lack of urgency that could prove detrimental in the future.
PQC Inaction and Comparison to Y2K
In 1999, as the world was speeding towards a new millennium, the Y2K Bug was on everyone’s mind. Because computers at the time stored the current year as only two numbers (99 for 1999, 98 for 1998, and so on), the fear was that once the year 2000 hit, computer systems around the world would interpret “00” as “1900” rather than “2000.” This bug was predicted to shut down critical infrastructure technology unless taken care of.
The hard deadline of January 1st, 2000, pushed organizations and governments to solve the problem before it was too late. An estimated $300 billion USD was spent worldwide to fix the bug, and, due to the hard work of thousands of workers behind the scenes, the impact of the Y2K bug was largely mitigated.
The Y2K bug is eerily similar to the newly dubbed Q-Day, the day quantum computers will break modern encryption. If/when this breakthrough event does occur, the implications will be far greater than those of Y2K, rendering the majority of modern encryption obsolete. So, why aren’t we seeing the same urgency to solve the Q-Day problem?
Quantum Doubt and Portrayal in Media
Unlike Y2K, quantum computing’s timeline and image make it harder to mobilize. There were a few traits to Y2K that enabled it to be taken seriously by not only the technology workers trying to fix the problem, but most importantly, by influential company executives.
The tangible deadline certainly helped executives take the problem seriously. Significant pressure was applied, pushing organizations to act sooner rather than later. In contrast, because Q-Day could be anywhere from 3 to 15 years away, according to analysts, it is challenging to convince organizations to allocate resources to the problem now.
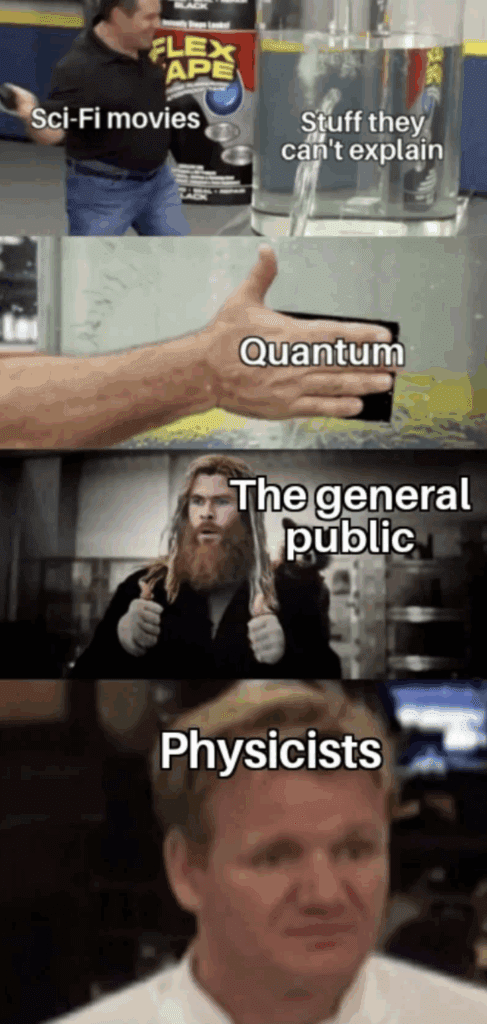
The way that the Y2K problem was comparatively easy to understand and quantify also had a large impact on how it was handled. The Y2K bug was easy to take seriously in part due to its mundane nature. In contrast, the quantum threat may seem technologically far-out to most, with some dismissing it entirely as science fiction due to the often-inaccurate portrayal of quantum technologies in popular media. Superhero movies, sci-fi adventures, and space operas all use the term “quantum” to describe just about anything adjacent to magic, causing “quantum” and “sci-fi” to share the same brain space.
This portrayal makes it difficult for outsiders to take quantum seriously. Ella Meyer, a quantum computing outreach coordinator at the University of British Columbia, told GeekWire that media portrayals like this are making it “harder than ever to get people to properly engage with this world.”
Executives and key decision makers around the world are still trying to wrap their heads around the equally sci-fi-like world of AI, and now they’re being told they must start dealing with seemingly outlandish quantum threats.

Because of the lack of a hard deadline and the fantastical portrayal of quantum in fictional media, it is easy to see how difficult it can be for non-technical decision-makers to take the quantum threat seriously.
Call to Action
It is vital to the security of all organizations to get executive minds on board with the quantum threat. This isn’t simply something to be ignored. Already, national post-quantum migration roadmaps have been released by the likes of Canada, the USA, and the UK.
The migration to post-quantum cryptography will be long and arduous for most organizations. Convincing an executive team to commit to a multi-year-long project defending against such a fluid threat will be difficult, but it is entirely necessary.
When discussing the quantum threat with executives, make sure to speak their language. Don’t get caught up in superposition and qubit count, but instead point to government migration guidelines and the post-quantum security plans of large corporations.
Additionally, highlight how migrating to post-quantum cryptography will improve an organization’s security posture beyond the quantum threat. Upgrading to new, improved cryptography, developing ways to become cryptographically agile, and undergoing a cryptographic discovery process will all help defend governments, businesses, and utilities against both quantum and classical threats.
An organization’s post-quantum cryptography migration doesn’t have to be handled entirely in-house, either. Recently, new and established vendors, such as IBM, PQShield, and SandboxAQ, have begun offering cryptographic discovery and post-quantum remediation services. For organizations with small security teams, such vendors provide essential assistance.
Conclusion
In a world where the status quo on security and technology is constantly changing, it can be challenging to sift through the noise and find what will truly make an impact. The Y2K bug was taken seriously because it was perfectly positioned to cut through that noise due to its hard deadline and grounded nature.
The quantum threat to cybersecurity is different. There is no hard deadline, no immediate observable impact, and it is obstructed by the mythological portrayal of a very real technology. Nevertheless, actions to mitigate this threat must be taken.
Every delay in migration extends the period in which critical data remains exposed to future decryption. The growing concern of “harvest now, decrypt later” attacks—where adversaries stockpile encrypted data anticipating quantum capabilities—makes early action essential.
The threat must be properly communicated to executive minds. Point to existing government migration guidelines, avoid getting caught up in the technical weeds, and make it clear that this is a threat that cannot be ignored.
Sources
- Boyle, Alan. “Get a Reality Check on Quantum Computing vs. ‘Quantumania.’” GeekWire, 16 Feb. 2023, www.geekwire.com/2023/reality-check-quantum-computing-quantumania/.
- The Editors of Encyclopaedia Britannica. “Y2K Bug.” Encyclopedia Britannica, Encyclopedia Britannica, inc., 4 Sept. 2025, www.britannica.com/technology/Y2K-bug.
- “Post-Quantum Cryptography: CSRC.” CSRC, National Institute of Standards and Technology, 2016, csrc.nist.gov/projects/post-quantum-cryptography.